- Ufed Physical Analyzer Crack
- Cellebrite Ufed Reader Download
- Ufed Physical Analyzer Full Crack Version
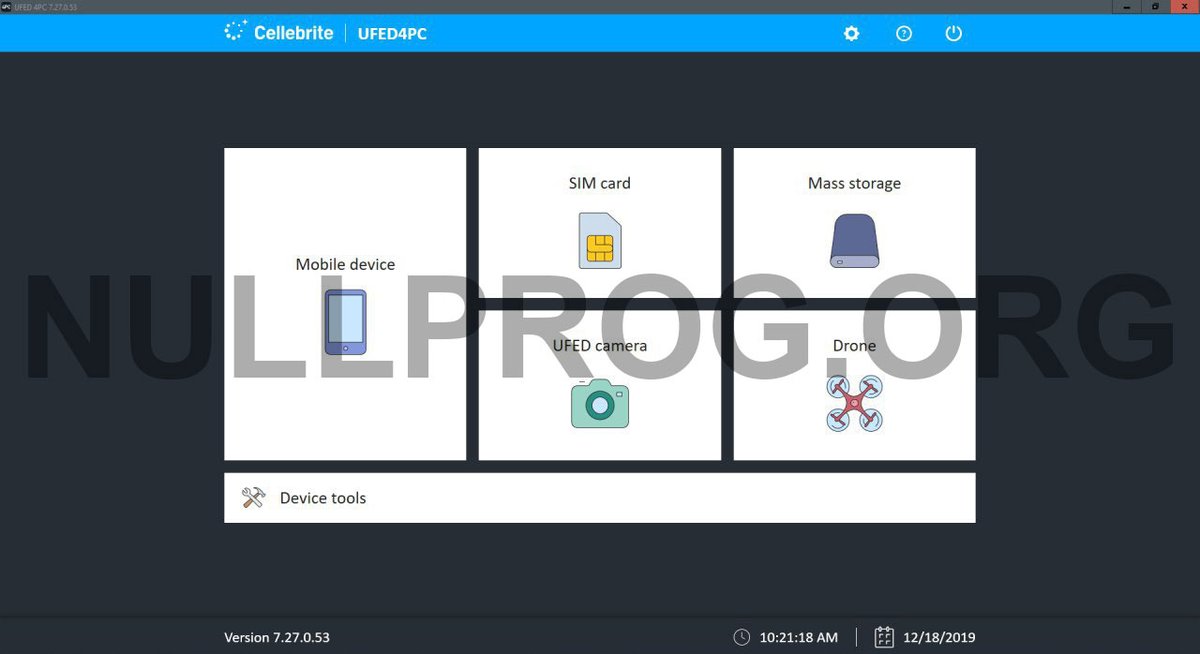
UFED 4PC Crack is Cellebrite’s software-based mobile forensic solution. It provides users a cost effective, flexible and convenient tool on their existing PC or laptop. Extend powerful extraction, decoding, analysis, reader and management capabilities to your teams with 4PC software.
Flexible and convenient, 4PC is a software-only platform that can be used on the hardware of your choice. Whether you’re examining in the lab, investigating in the field, reviewing findings in an office or managing your digital forensics tools in an IT department, 4PC offers easy deployment to a PC, laptop, server or other hardware to meet your specific requirements.
The UFED Logical Analyzer's rich features are only a small fragment of the UFED Physical Analyzer capabilities. Once a user upgrades from a logical license to an ultimate license, the software will be upgraded to the UFED Physical Analyzer. Cellebrite announced update their software. Cellebrite license crack, ufed 4pc crack, crack ufed physical analyzer. Unlocking, extraction, decoding and analysis of data from devices, applications. ️Request Crack (Software Cracking Service) Dongle Emulator Clone. Download Cellebrite UFED Full Version Cracked, ufed 4PC, UFED Analyzer Ultimate, ufed physical analyzer crack, Analytics Desktop optimizes and extends your existing mobile forensic investments. It also serves as an essential building block to creating an end-to-end unified investigative platform from a partner you can. In UFED 7.34, we are happy to introduce first-time support for a generic full file system or physical extraction for unlocked Qualcomm based Android devices. The new Qualcomm Live capability extends access to the latest devices from vendors such as Xiaomi, OPPO, OnePlus, VIVO, Nokia, LG Motorola and others, running OS versions 7 up to 10.
UFED 4PC Features
- UFED Device Adapter
- UFED Carrying Case
- Tip & Cable Set
- Tip & Cable Organaizer
- UFED Memory Card Reader
- Multi SIM Adapter
- UFED SIM ID Cloning Card
- Micro SIM ID Cloing Cards
- Nano SIM ID Cloning Cards
- Phone Power-up Cable
- Cleaning Brush for Phone Connectors
- Tip Velcro Strap
- Spare Tips Cartridge
- USB Flash Drive
- USB Extension Power-up Cable
Developer :Website

Ufed Physical Analyzer Crack

Software Version
Cellebrite UFED 4PC 7.40.0.85 – Latest version
Want BUY in much lower price?
E-mail : nullprog.exe@gmail.com
Also Visit UFED Physical Analyzer Software : UFED Physical Analyzer
Proof
Keyword
UFED 4PC Emulator and Dongle Emulation
UFED 4PC Crack and Keygen
I realize it’s been awhile and these tools have really changed since my last post in 2015. Have they changed for the better? Not necessarily. Some tools update so quickly that they lose the basics. For that reason, please test and validate your tools and never trust what is advertised. Your goal should be to determine how the artifacts were placed on the device, not that the artifact exists on the phone. By this I mean – how did it get there? Did the phone suggest it, the user searched for it or was it synced to the device? This level of analysis is something your tool cannot do for you, which is why you probably read blogs like this and learn what you can trust and where you must apply your smartphone skills.
One of the most common questions I am asked is “which tool is the best?” Guess what? There isn’t just one! And I strongly recommend you use more than one, especially for analysis and sometimes even for acquisition (read my blog on iOS 11 from Oct. 2017). These tools are picky and seem to like one device better than another and parsing is not the same across the board. You must know the tool strengths and be able to defeat the weaknesses. To help you out, I am listing the tools that I prefer and my reasons why. These tools are not perfect and they DO NOT have a “Find Evidence” button. Is your tool missing from this list? Offer me a demo and I will try to find time to test it and give feedback. 🙂
As I stated in the last blog I wrote on this topic, I am not going to delve too much into acquisition tools and methods. There are so many out there. Some of the ones I rely on to get my data are Cellebrite UFED (not for iOS devices), Cellebrite Physical Analyzer (for iOS devices), Oxygen, iTunes and my good ‘ole Mac. I always tell my students to try everything when you have a smartphone on your desk. You don’t know how that device was used and what settings are already enabled behind that locked device. You may surprise yourself when you are able to grab everything with the click of the “acquire evidence” button on your tool of choice. However, it’s not always that easy so verify that you have unencrypted data even if you get a dump. Additionally, I recommend you always get a physical dump and logical or backup to help you parse the data. Make sure you test your tools and test them often. Don’t let one hurdle knock you down.
The list below doesn’t include all smartphone tools, but simply the ones I rely upon. If you have others you like, please comment and share. I love hearing what others are using because I don’t have time to test every tool and keep up with the quickly released updates. So, help me out here.
The Heavy Hitting Commercial Solutions (Not in any particular order):
*NOTE: DO NOT RELY ON YOUR TOOL TO TELL YOU HOW DATA WAS PLACED ON THE DEVICE—THAT REQUIRES YOUR KNOWLEDGE! VERIFY ALL LOCATION ARTIFACTS!!!
- Magnet – IEF Mobile – Great for Internet evidence and parsing 3rd party application data. One of the best iOS app parsers out there. AXIOM is now the up and coming tool, but does have some growing pains, so test it for yourself. In both of these tools, the Custom/Dynamic App finder is so useful as location additional databases of interest that you should examine for relevance. This tool easily ingests image files from other tools.
- Physical Analyzer – Probably the best analytical platform out there specific to smartphone tools. It doesn’t parse everything, but it gives us a platform for analysis where we can leverage it find the evidence with some manual carving and hex searches. PA doesn’t seem to omit files it doesn’t understand, which seems to be happening in other tools. Best physical search feature for locating data in raw hex, other than in file system dumps of iOS devices. The new fuzzy models plug-ins are fantastic as they identify databases commonly associated to 3rd party applications that aren’t parsed by the tool. This tool easily ingests image files from other tools.
- MSAB XRY/XACT – One of the only tools that consistently provides access to the raw files (databases, xml, dat, plists, BLOBs, etc.) during a logical acquisition. Guess what, to recover data that the tools don’t parse you need the raw files. This tool give you access to them! XRY is strong at parsing strange backup files from smartphones, such as those created with Samsung Kies.
- BlackLight – Great tool that can run on a Mac or PC! Primarily supports iOS devices, but I have seen students force load Windows Phones and Android devices into the tool to use it as a file system examination platform. However, it was designed to support iOS devices. Haven’t you heard that you should examine a Mac with a Mac? A wise examiner once told me that and it still resonates with me. This tool uniquely pulls out Google Maps and Apple Maps searches that the other tools commonly misinterpret. If you hear me talk about BlackLight, you know that I rave about the Windows hard drive support. Strange that the Mac guys are doing so well on Windows. 😉
- Oxygen – This is one of my new favorites because I am constantly examining 3rd party applications. This tool highlights files the applications use and where they are stored. Guess what? That list is now your cheat sheet. Pretty sweet! I also love the built in PLIST Editor (hex and xml views) and the SQLite editor. This is the best tool for BlackBerry and BlackBerry 10 devices. It acquires the event log and provides a secure way to create a BB backup file. Also counts out all those nasty little databases for you. I wrote a recent blog on Oxygen, so read it if you want more details on this tool. Just like most of the others, there are growing pains, so test it and validate that it’s showing you all of the data.
- Elcomsoft – I use the Phone Password breaker to crack locked BlackBerry device, BlackBerry and iOS Backup files. I also use this tool to pull cloud data. It’s awesome! Runs on both a Mac and PC.
The Other Guys (Not free, but not as expensive as the heavy hitters):

Not in any particular order…
Cellebrite Ufed Reader Download
- Andriller – This tool can crack passcodes for locked Android devices and provides logical parsers for iOS, Android and Windows 3rd Party Application files. Free for LE and well worth it for everyone else. The fee is small the results are huge! https://andriller.com/
- Sanderson Forensics tools – Great SQLite support! The SQLite Forensic Toolkit is so useful in recovering deleted data and for converting those pesky timestamps. I love how this tool shows you how the queries are run and what’s happening when you press a button. New to SQLite forensics – start here! Stay tuned for Pauls’ new SQLite Forensics book (it’s fantastic and is not a sales pitch for his tool!) Paul will provide a free demo upon request. http://www.sandersonforensics.com/forum/content.php
Ufed Physical Analyzer Full Crack Version
Open Source and Other Solutions:
Parsers developed by the community. These people are rock stars and often give back by developing scripts to help us sift through application and smartphone data. Check out their blogs and githubs to get the latest scripts that I rely on to parse the massive amounts of data the commercial tools just don’t support.
- Mari DeGrazia (http://az4n6.blogspot.com/)
- SQLite-Deleted-Records_Parser – A must have for unveiling deleted data in SQLite databases.
- Adrian Leong (http://cheeky4n6monkey.blogspot.com/)
- His blog rocks! Adrian hits on hard topics. Read it! (HEIC/HEIF on iOS 11 is one of his latest). Also, all of his scripts have been tested to work in the SANS SIFT.
- Honestly, he has so many scripts out there – go check them out! (Facebook Messenger, SQLite parsers, coordinate converters and more!)
- Jon Baumann was a student of mine recently who decided to build scripts to fix the things that were broken in the tools. LOVE THAT! https://github.com/threeplanetssoftware/
- His new sqlite-miner script parses databases containing BLOBs that contain human-readable data. Not only does it identify the contents, it parses them and exports them!
- Autopsy – The Android Analyzer module hasn’t been updated in a while, but it still supports parsing some items from Android devices. It also gives you access to the File System directory tree faster than any commercial tool out there. Most tools make you wait to see the file system during parsing – not Autopsy. Also, the keyword searching and carvers are top notch. http://sleuthkit.org/autopsy/
- iBackupBot – Great for parsing iOS backup files. Works on both Macs and PCs. Make sure you have the latest version that supports iOS 10 and 11.
As I always say, I am sure I have forgotten to give credit to some where it’s due, so I am requesting that you help me out. What tools really help you and how? Is there one script that you found and cannot live without? Do you use something more robust than a Java decompiler for mobile malware? Is there something parsing double Base64? Don’t know what that means??? Take FOR585 and Cindy Murphy, Lee Crognale and I will teach you. Our course is offered almost every month and all over the world. Check it out for585.com/course.
Keep digging in that Hex! The data is there and it’s your job to find it.
Comments are closed.